Prefer a PDF?
We created this case study as a web page for better mobile optimisation and accessibility. If you'd still like a PDF version of this use case, you can download it here:
THE CHALLENGE
In the expansive world of O&G, every upstream and downstream environment pipeline, refinery, and retail unit relies heavily on Industrial Control Systems (ICS) to maintain safety and consistency. But the march of technology—sensors, processing power, remote operations, and IoT—brings a fresh set of challenges, intensified by the contrasting priorities of OT and IT departments.
On this project, we tackled legacy equipment relying on SPAN ports and unidirectional gateways that demanded unique solutions for network safety. With remote sensors peppered in distant fields, safeguarding virtual environments against cyber threats was crucial. Plus, meeting international standards, like the EU Cybersecurity Act, was non-negotiable.
Dive into this case study to uncover how we turned these intricate challenges into opportunities for innovation and advancement, maintaining a balance between technology and regulations while keeping the operations secure and efficient.
THE GOAL
In the customer's journey to re-envision network design, it became clear that Garland's innovative solutions addressed their prevailing challenges directly. The core objective of this endeavour is multifaceted: to introduce secure visibility into an aging infrastructure, to streamline connectivity, and to amplify performance. More than just a technical enhancement, this project serves as a vital bridge between OT (Operational Technology) and IT (Information Technology) teams. By doing so, it not only fosters interdepartmental collaboration but also strengthens the bulwark against looming cybersecurity threats. Discover the transformative power of technology that safeguards and unifies.
THE SOLUTION
Harnessing the unique blend of fibre and copper connectivity, Garland Technology's forward-thinking visibility architecture adapts to both 1G and 100M network speeds. Strategically designed, it not only encompasses diverse OT infrastructures across various locations but also integrates switches with SPAN ports for comprehensive monitoring.
- Added Security Layer: A standout feature? The capability to channel network traffic directly to an Intrusion Detection System (IDS) sensor ensures you're always one step ahead of potential threats.
- Why This Matters: In our digital-first age, a secure and flexible network is non-negotiable. Garland Technology's solution guarantees this, offering adaptability and top-notch security in one package. Enhance your network's resilience and efficiency, and step confidently into the future with Garland.
- Takeaway: Embrace the innovation that's both dynamic and secure. Explore Garland Technology’s cutting-edge visibility architecture today.
ADDED SECURITY
Garland Technology recommends installing network test access points (TAPs) to ensure that all monitoring feeds copy and transmit 100% of the network traffic to monitoring tools. A monitoring tool can only perform effectively and consistently when it receives every data packet. TAPs are independent and invisible to the network, passing all 7 layers of OSI network traffic, including layer 1 and layer 2 errors. TAPs do not have an IP or MAC address, making them unhackable. When enhanced with Failsafe technology, TAPs deliver power redundancy without being a failure point in the network.
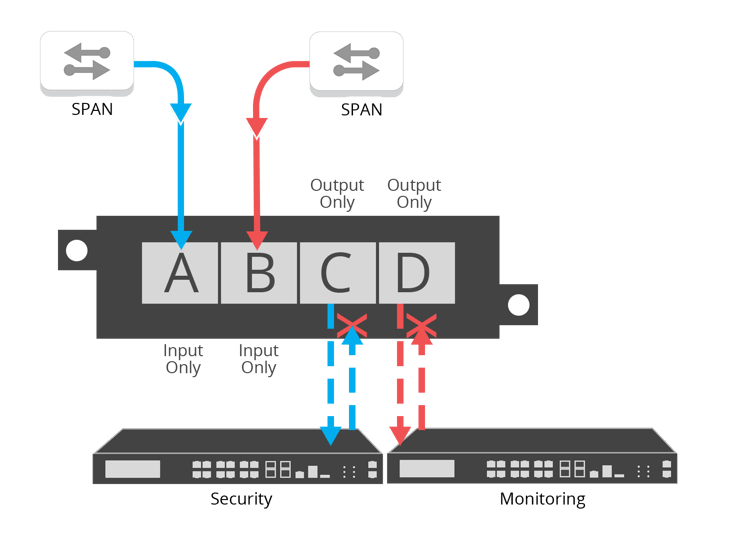
For unidirectional gateway segments, Garland Technology's Data Diode TAPs ensure data is never injected back into the network by forcing traffic to flow in a single direction. When traffic is locked in a unidirectional path, there is no risk of data flowing back into the network, eliminating security risks. This is a crucial component in ensuring information security and protecting critical digital systems, such as SCADA/industrial control systems, from inbound cyber attacks.
REDUCING NETWORK COMPLEXITY
Many companies in different industries face challenges with complex architectures. When adding requirements from both OT and IT, industrial environments need to reduce complexity to streamline performance and facilitate future growth.
For example, we encountered a web of existing SPAN ports, which were their primary packet capture solution. This added a layer of complexity and created blind spots for the monitoring tool, as dropped packets were a common occurrence. Additionally, the SPAN links were often misconfigured or turned off, unintentionally transmitting zero network traffic to the monitoring tool.
A good best practice is installing TAPs between the switches on each network segment if SPAN port usage is required. This will provide safeguards and prevent performance degradation of the switch. Network TAPs make it easy to manage access points in the network to instrument and deploy new monitoring and security tools. If you still need to use some SPAN links, Aggregator TAPs allow you to consolidate them into just one or two links.
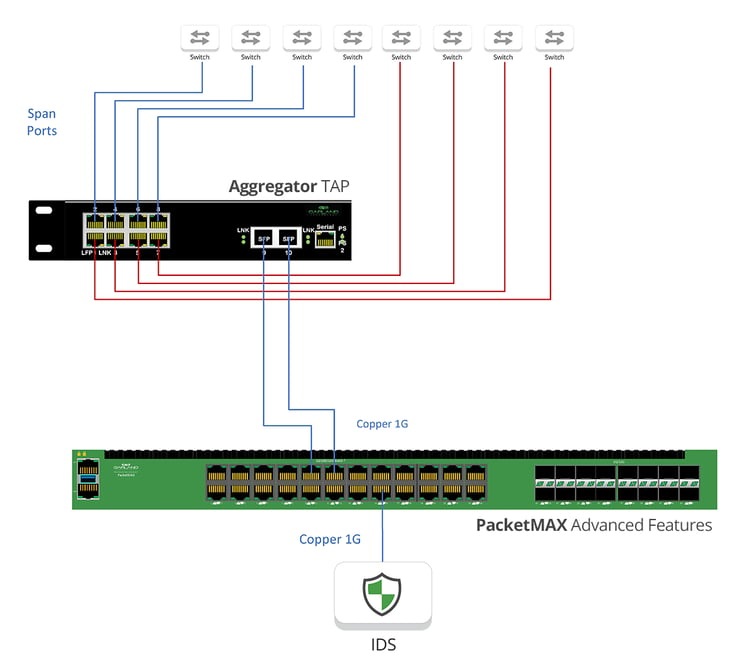
The next step in optimising network complexity was adding an aggregation layer to manage all of these links. Garland's PacketMAX packet brokers aggregated, filtered, and load-balanced the TAP traffic, streamlining the data collection for analysis during troubleshooting or security incident response. This allowed OT and IT to access the data they needed at the right time.
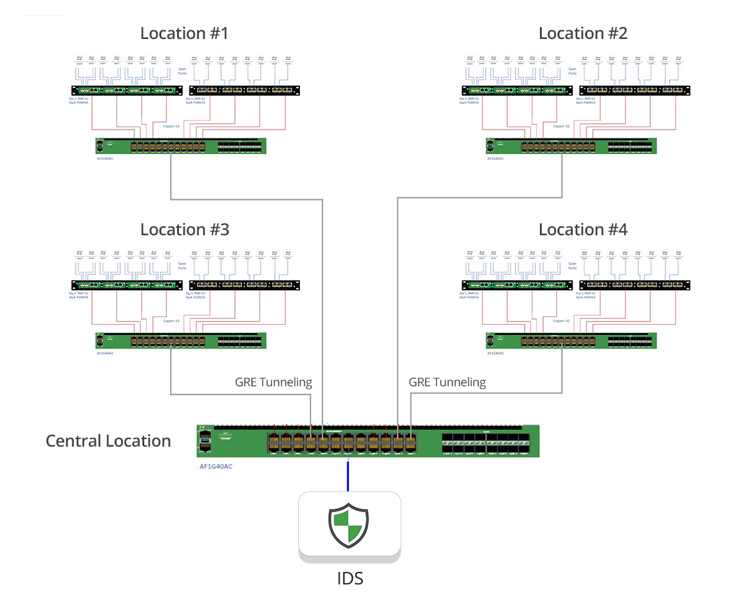
With multiple sites, Garland's PacketMAX can move traffic from one location to another through Tunnel Encapsulation (GRE, L2GRE). This creates the ability to connect individual power stations to a master control location or even another power station. The monitoring tool can be located separately from the network being monitored because tunnel encapsulation can send monitored traffic from one location to another. This provides cost savings by reducing the quantity of monitoring tools required and delivers redundancy should a monitoring tool within the network fail.
With their recent virtualized SCADA deployments, they faced drastically reduced visibility and blind spots in their remote operation VMs. Deploying Garland Prisms traffic mirroring eliminated these data blind spots, providing the SCADA platform and other connected system access and visibility. Adding our new air-gapped private solution and TLS encryption option provided the added security assurance they were looking for.
Implementing a proper network visibility fabric for this oil and gas company provided the OT teams with enhanced productivity, accelerated service degradation or downtime resolution, and improved IT/OT collaboration. Network aggregation improved network performance and ROI by reducing administrative overhead, improving data quality, and improving tool collaboration and data sharing while reducing the cost of the overall visibility solution.
THE BENEFITS
- Reduce network complexity and administrative overhead
- Enable infrastructure upgrades
- Improved the network performance
- Improve the effectiveness of tool performance
- Added infrastructure security
Looking to add visibility and reduce network complexity but not sure where to start?
IT'S EASY TO GET STARTED
Join us for a brief network Design-IT Demo or consultation. No obligation - it’s what we love to do.
